Understanding Compromise Assessment: A Critical Layer in Cybersecurity Defense
Introduction
In an era where cyber threats are increasingly sophisticated, organizations often implement layered defense strategies to protect their digital assets. However, despite these multiple levels of protection, breaches can still occur, often slipping past unnoticed. This is where compromise assessment becomes essential. The primary objective of compromise assessment services is risk reduction. They help organizations discover active cyberattacks and identify sophisticated attacks that may have occurred in the past through various methods, including:
- Tool-assisted scanning of all endpoints
- Host and network equipment log analysis
- Threat intelligence analysis, including darknet searches
- Initial incident response to contain discovered threats
In this article, we will explore real-world cases from our practice where organizations, despite having numerous security controls in place, still found themselves compromised. In each instance, compromise assessment served as the last line of defense, successfully detecting incidents that had evaded other security measures.
Patch Management Issues
One of the most common root causes of security incidents identified during compromise assessments is inadequate patch management. The process of vulnerability patching can be time-consuming for various reasons, from the release of a patch to identifying vulnerable assets and ensuring proper application. Factors such as business continuity requirements—like the inability to reboot servers without downtime—can further delay this process.
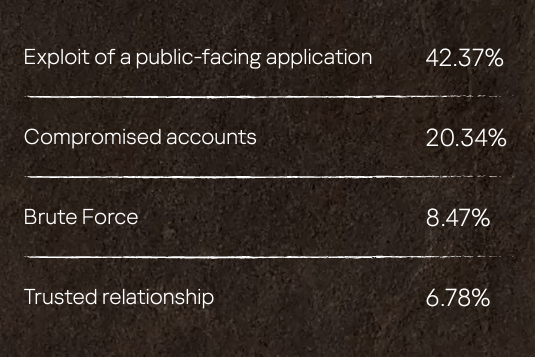
According to the Kaspersky Global Emergency Response Team (GERT) in 2023, exploitation of public-facing applications was the root cause in 42.37% of incidents investigated. In one case, a web server was patched a month after an attacker infiltrated the network. This delay provided a window of opportunity for the threat actor, who deployed a SILENTTRINITY C2 stager immediately after compromising the server. Within days, they attempted to dump credentials and conducted internal reconnaissance until they obtained the domain administrator’s credentials.
Policy Violations by Employees
While organizations often focus on external threats, internal policy violations pose a significant risk. Research indicates that 51% of SMB incidents and 43% of enterprise incidents involve IT security policy violations caused by employees. In one of our compromise assessments, we traced an incident back to a contracted cybersecurity consultant. During a meeting with the customer’s board, we presented a list of compromised accounts, revealing that 71% belonged to the customer’s employees, with a significant portion accessible from outside the company.
The investigation revealed that a C-level officer’s account was compromised due to credentials leaked from a third-party consultant’s machine. This incident could have been avoided by ensuring that all employees and third parties adhered to established security policies.

MSP/MSSP Issues
Managed Security Service Providers (MSSPs) often focus on continuous monitoring and alerting but may overlook critical aspects such as detection gap identification and visibility enhancements. For instance, a common oversight is the failure to enable the X-Forwarded-For HTTP header on web servers, which can obscure the original IP of connections and complicate incident investigations.
In one case, our compromise assessment revealed that an external Security Operations Center (SOC) had missed multiple webshell detections on a server over several days. The MSSP’s analysts failed to raise alerts because the malware was deleted by antivirus software each time it was detected. This oversight allowed the attacker to continue probing the network until they found a webshell that evaded detection.
Incomplete Incident Response
Effective incident response is crucial for eradicating threat actors from networks. This process involves several actions, including:
- Removing malware, scripts, tools, and backdoors installed by the attacker
- Changing passwords for compromised accounts
- Rolling back system configurations that may increase vulnerabilities
Even after malware is removed, forensic artifacts may remain, leading to the discovery of past attacks during compromise assessments. In one instance, our analysts identified a suspicious Group Policy modification in Active Directory that allowed reversible password encryption, enabling attackers to dump credentials in plaintext.

False Sense of Security
Organizations often operate under a false sense of security, believing that their cybersecurity solutions are foolproof. However, the effectiveness of even the most advanced products relies heavily on proper installation, configuration, and integration. Without these, organizations cannot fully leverage their cybersecurity tools.
In our assessments, we have encountered cases where specialized scanners deployed alongside existing antivirus/endpoint detection and response (EDR) solutions uncovered threats that went undetected. Issues such as the absence of detection rules, outdated malware signatures, and shadow IT practices left certain servers unprotected.
Conclusion
Compromise assessment has emerged as an indispensable component of a comprehensive cybersecurity strategy. The cases discussed illustrate that no security measure, regardless of its sophistication, is entirely infallible. From internal policy violations to patch management failures and overlooked misconfigurations by third-party service providers, the risks are diverse and often hidden in plain sight.
Integrating compromise assessment into the security framework enables organizations to uncover these hidden threats, address vulnerabilities, and strengthen their overall security posture. In a landscape where cyber threats are constantly evolving, the proactive identification and mitigation of potential compromises are not just advisable but essential. This approach ensures that organizations are not merely reacting to breaches but are continuously verifying the effectiveness of their defenses, thereby reducing the risk of undetected compromises and safeguarding their assets more effectively.
